ShodhKosh: Journal of Visual and Performing ArtsISSN (Online): 2582-7472
|
|
Digital Bodies and Social Protection: Visual Culture, Gendered Cyber Threats, and Policing Narratives among University Youth
Eram Rizvi 1![]()
![]() ,
Dr. Kaushik Mishra 2
,
Dr. Kaushik Mishra 2![]()
![]() ,
Dr. Aparna Vajpayee 3
,
Dr. Aparna Vajpayee 3![]()
![]() , Ankit Kumar 4
, Ankit Kumar 4![]()
![]() , Dr. Vishal Sharma 5
, Dr. Vishal Sharma 5![]()
![]()
1 Research
Scholar, University Institute of Media Studies, Chandigarh University, Mohali,
Punjab, India
2 Professor,
University Institute of Media Studies, Chandigarh University, Mohali, Punjab,
India
3 Professor, School of Liberal Arts and Management, P P
Savani University, Surat, Gujarat, India
4 Research Scholar, University Institute of Media Studies, Chandigarh
University, Mohali, Punjab, India
5 Assistant Professor, Department of Journalism and Mass Communication, Ram
Lal Anand College, University of Delhi, India
|
|
ABSTRACT |
||
|
The blistering
development of digital spaces of visual media has transformed the experience
and presentations of bodies, identities, and vulnerabilities on the Internet,
especially through young people in universities. This paper focuses on
analyzing the gendered cyber threats against women in light
of visual culture and social protection, which concerns the perception
and formation of policing narratives in online space. Based on the answers of
Gen Z female university students, the study examines the experience of
cybercrimes against women, its perception, and visualization in the social
media, online platforms, and mediated discourse. The paper makes cyber
harassment a part of modern visual culture in which images, acts of
subjectivity and the relationship in the Internet
help produce vulnerability and resistance. It also examines how the law
enforcement is depicted in digital discourse, identifying the disjunction
between protection mechanisms carried out by the institutions and how the
youth understand safety. The integration of visual studies, gender studies,
and cultural analysis perspectives will give the research a step forward to
predict the nature of cybercrime visually by performatively, as well as in
representational aspects. The results indicate that visual stories have a
strong impact on awareness, reporting behavior, and trust in the policing
structures. The present research is an addition to an emerging framework of
literature on digital bodies and social protection by providing information about
the utilization of visual culture with the help of preventive measures,
awareness-raising activities and creative interventions to tackle gendered
cyber threats in the current youth cultures. |
|||
|
Received 21 September 2025 Accepted 25 December 2025 Published 17 February 2026 Corresponding Author Dr.
Vishal Sharma, vishalchsm@gmail.com DOI 10.29121/shodhkosh.v7.i1s.2026.7191 Funding: This research
received no specific grant from any funding agency in the public, commercial,
or not-for-profit sectors. Copyright: © 2026 The
Author(s). This work is licensed under a Creative Commons
Attribution 4.0 International License. With the
license CC-BY, authors retain the copyright, allowing anyone to download,
reuse, re-print, modify, distribute, and/or copy their contribution. The work
must be properly attributed to its author.
|
|||
|
Keywords: Gendered Cyber Threats, University Youth, Social
Protection, Cyber Harassment, Visual Mediation, Policing Narratives, Digital
Vulnerability, Youth Agency, Online Safety |
|||
1. INTRODUCTION
The digital spaces have been reduced to key arenas where bodies, identities and social relations are constructed, negotiated and competed, especially in the everyday engagements of the youth in universities whose interactions are mediated through the use of images. The circulatory speed of images, selfies, short-term video, screenshots and symbolic acting of identity does not only mimic the experience of visibility, vulnerability and belonging in modern youth-culture but also does so extensively and replenished across networked spaces Evans and Ringrose (2024). In such spaces, gendered experience of cyber harassment, surveillance, and symbolic violence also expresses the attributes of larger hierarchical structures but also creates new avenues of risk on the platformed communication. The digital image of women is often put to test, distortion, and intimidation which helps to see that visuality both functions as a way of acting out and a platform upon which power is enforced Bucher and Helmond (2017). Online harm experiences, thus, are not confined to specific legal offenses but are reflected within culture, emotional reactions, and peer-mediated senses of interpretation that determine categories of awareness, reporting, and coping actions.
Figure 1
Figure 1
Conceptual Framework
Diagram Linking Digital Bodies, Cyber Threats, And Social Protection
The space of the university can be perceived as a specific place to explore the operation of such dynamics because of the existence of a complex of the institutional, social, and technological institutions on Gen Z students that shape the image of the sense of security and safety. Connection to formal structures such as cybercrime reporting, campus support systems are typically twisted with digital language, memes, and distributed visual accounts that create mutual epistemologies of policing and responsibility Ringrose et al. (2022). The confidence in social protection is found not just in the policy effectiveness but also in the way the protection is framed, told and experienced emotionally in youth networks. Viewing culture as a way of knowing more about the reasons behind some threats go unreported, industrial reaction possibly seem distant and resistance practice building up through creative and collaborative expression Schellewald (2023). A cross-disciplinary approach that blends the visual studies, gender analysis, and socio-legal awareness can provide the means of understanding gendered cyber threats as lived-in cultural existence instead of the abstract regulation issues and suggesting the alternatives in the way of more responsive and youth-oriented forms of cyber social protection.
2. Digital Bodies and Visual Culture in Youth Online Spaces
Networked visual spaces serve as key arenas in which young people in the digital era build, perform and establish embodiment in digitally mediated life. Platformed spaces do not confine visuality to representation but instead actually generate social meaning through the way bodies become visible, desirable, vulnerable, or excluded within platformed space being shaped by algorithms Sheth et al. (2022). Photographs, short-form videos, avatars, filters and aesthetic performances are symbolic extensions of the self, which allow young consumers to bargain identity in changing contexts of peer awareness, surveillance, and platform regulations. Digital embodiment consequently appears as a process of relational and performative interaction in which the body is consistently put together in images, gestures, captions and feedback of the audience Goodyear et al. (2021). These processes dissolve boundaries between physical presence and mediated appearance and establish hybrid forms of subjectivity in which the emotional experience, social confirmation and risk exposure cannot be separated whilst circulating through the visual. These visual economies within the culture of youth in universities are being bound up with belonging, popularity, and self-expression, as well as subjecting individuals (especially women) to increased scrutiny and gendered judgment in both the wider cultural power dynamics Whitehead and Ringrose (2021).
Figure 2
Figure 2
Showing
Relationships Between Youth Perception, Cyber Threats, And Institutional
Response
Platform performance is a subject that is highlighted by theoretical insights in visual culture and feminist media studies to reveal how the politics of looking and being seen are altered. Visual practices multiply normative expectation about femininity, respectability, attractiveness, and even allow resistance in the form of parody, counter-aesthetics and shared narration Biradar et al. (2025). Embodiment in the digital space, therefore, works in a conflict between agency and control: users are free to manage self-presentation, but the aspect of the algorithmic prominence, permanence of screenshots, and participatory surveillance limits the sense of autonomy. Platform infrastructures also facilitate these dynamics with the privilege of engagement metrics, sensational imagery, and inculcating commercial logic in the normal self-representation. Shame, validation, harassment or solidarity experiences are perceived to be largely influenced by technological design and not necessarily as a result of interpersonal interaction Angrish et al. (2024). The concept of digital bodies in youth online contexts thus needs the consideration of intersection of visual performance, gendered cultural norms and socio-technical governance. This approach offers essential background to exploring the manifestation of gendered cyber threats in visual circulation, and the importance of social protection focusing on the legal force but also the cultural and affective economies according to which digital embodiment is experienced and negotiated.
3. Gendered Cyber Threats—Forms, Experiences, and Visual Mediation
Gendered cyber uncertainties in youth cultures of universities are developed over a continuum of practices that moves beyond the individual incidences of abuse to patterned forms of digitally mediated abuse. Sexual messaging pre-emptively, not with social permission, spreading images without consent, doxing, posing as someone else, coordinated trolling, stalking with screenshots and reposted imagery are all common forms of harassment. Platform affordances further intensify such practices, favoring iconic replication, anonymity and amplification of a following, whereby such might wreak havoc due to their rapid transit across societal platforms that came with little to no responsibility Seguin et al. (2021). Verifying accounts of such that are always provided by university student accounts which show that fear or humiliation are behaviors that may and often are long term conditions which may be anticipatory anxiety as reflected by the possibility of coming under it. This permanence and shareability of digital images that makes everyday, mundane self-presentation a potentially vulnerable issue and particularly in the situation where it concerns women whose presence on the Internet tends to be sexual, evaluated, or otherwise weaponized, as a peer culture. Gendered harassment consequently functions on interpersonal, community and technological tiers, creating both cumulative and overlapping experiences of emotional distress, reputational danger and limited engagement in a digital public life. Visual mediation is also conclusive in the perception, circulation, and normalization of cyber threats. Screenshots, edited photographs, memes and brief video clips are seen as components of an evidentiary artifact, instruments of intimidation, as well as the vehicle of social shaming, and incorporate harassment in the visual storytelling actions that obscure the line between documentation and spectacle. Such imagery is repeated many times, a factor that leads to cultures of desensitization where cruel actions are normalized as entertainment or commentaries Bhandari and Bimo (2020). Simultaneously, the circulation of visuals can facilitate solidarity and opposition in cases where survivors exchange their experiences, organize peer support or oppose abusive discourses with the use of counter-visual imagery. Student reactions to report cybercrime show that the perception of threats mediated by visual values heavily informs the decision to report it in the context of peer communication and props the institutional actors are competent in interpreting such mediated harms. The inaccuracies between the experienced visual perceptions and the formal legal categories tend to dishearten reporting, causing silence and informal coping mechanisms. The visual mediation, empirically viewed, is, therefore, culturally mediated in both platform engineering, peer definition and the use of symbolic forms, making it necessary to design methodologies of social protection of the visual and affective meanings of digital abuse as well as legal definitions.
4. Visual Narratives of Policing and Social Protection
The role of visual culture in defining how the underage students of the college see policing, security and system security in the digital space is ultimately bargaining. Interactions with law enforcement are no longer a way of interaction or exchange as filtered through the diffusion of images, brief videos, news, memes, and posts that testify, which, when aggregated digitally, create symbolic images of authority. The emotional responses such as trust, distrust, assurance or fear are influenced with these visualizations even before the interactions with the formal reporting systems happen individually. When it comes to students (and especially to female students who face the gendered internet threat), the sense of protection is not so outlined by the legal frameworks as it is manifested by peer-to-peer digital space of policing. Delay in responsiveness, commentary, or insensitivity with the bureaucracy photos may intensify an experience of alienation to institutional care, or the accounts of undertaking care, promptness to cybercrime, or survivor-direct communication may make individuals believe to the capability of the social security. This visual storytelling is, therefore, a significant matter of legitimacy negotiation, policing is emotionally reorganized as an administrative, as opposed to a cultural, interpretation, a location in the daily media consumption.
Figure 3
Figure 3
Comparative
Framework Diagram Contrasting Institutional Messaging with Youth Visual
Interpretation
It is also the institutional perception that is emerging due to the clash of the formal way of communication and the affectionate language of the youth digital culture. Official warnings, press releases, or executive practices may be disseminated in dogmatic written formats that are not attractive to the visual epithelial platforms where symbols, words and emotional immediacy constitute the significance. Peer based explanations, commentator influence or first person accounts are mostly used by students in order to explain to themselves processes of cybercrime and thereby create alternative knowledge networks, which can either build or undermine institutional credibility. Social protection credibility is made thus through representational congruence: the more institutional communication becomes reflective of experience and acknowledgment of gendered vulnerability the higher one credibility; the more abstract, privileging, inarticulateness, the more inarticulateness. The visual narratives also play a role in anticipating accountability and privacy and responsiveness which will determine whether the youth will be empowered by reporting them or feel threatened. Research of such mediated perceptions reveals that the provision of social protection in the digital world should not be only efficient in processes but also needs to be culturally sensitive expressive manifestation that can be appealing to the young generation in the symbolic spaces where the meaning, safety, and power are conjointly remodel.
5. Gaps Between Institutional Safeguards and Lived Digital Realities
The membership structures configured to deal with cyber-criminal behaviors and to protect the vulnerable members will usually travel at legal definitiveness, procedural reporting schedules, and official investigation calendars which very significantly differ with the freshness, visibility, and emotive tincture of lineage of computer-based infliction done over an underage user of the university. Even though policies are based on documentation, jurisdiction, and levels of evidence, the students have been exposed to the cyber threat as the direct extension of identity, reputation, and psychological safety in the ever-networked state. It is this deviation that generates a structural distance in which the protection structures appear foreign and time alien to experience. The women who are harassed in a gendered manner usually understand the processes in the institution to be slow and opaque or may not necessarily be responsive to the reputational experience of visible circulation and this is more so when the harmful content is circulated faster than the formal counter mechanisms can respond to such circulations. This then results in informal coping that may be blockage of perpetrators or a set-off of platforms or a social network in preference to employing formal reporting procedures. Such adapting activities do not amount to denying protection but to the feeling that these stanzas of institutional protection are being disjunctive with the strains and definitions of the digital life.
Figure 4
Figure 4
Illustrating
Pathways from Threat Experience to Reporting
Youth perception suggests also that the structural disconnections not only cease at the response time, but also at the communicative style, accessibility, and symbolic appreciation of harm. The conceptualizations of cyber incidences are usually developed using institutional language that is either technical or legal in tool and can never bring out the affective dimension of humiliation, fear, social isolation and numbness due to visual exposure. Absence of reflection of the students in the official discourse weaken the belief in protection and lead to the redirection of the chain of underreporting and mistrust. Social implications Digital traces such as screen shots and memes or manipulated pictures can exert a significantly huge effect within peer networks, although are yet to be defined by legal processes that further increase the sense of the lived worlds being incomprehensible by institutions. The holes in the structures therefore become twice as distant as far as the temporality, representation and the knowledge is concerned how swift the saving can be, how the damage can be differentiated and the knowledge of whom is authorized as official one. In order to redress such disconnection, reconsideration should be made that social protection can be a responsive system culturally that can capture visual, emotional, and relational elements of cyber harm in addition to legally implement them. Such a change is necessary in its role of regaining trust, improving reporting behaviour, and ensuring the institutional protections have some substance to the digital circumstances that characterize the nature of youth vulnerability in the contemporary world.
6. Real-Time Case Studies
Digital aspect results in environments of oppression that are real time in nature in which gendered threats on the cyber space are realized through rapid actions on visual media, and cause immediate social, emotional and reputational harm to the university youth. Following the experience of students in a one-on-one manner, it has become apparent that the situations may start with an apparently run-of-the-mill activity, such as posting pictures, trending on a short-video, or posting publicly and then move toward its unchecked sharing, sexualization of material or targeted in itself. Screenshots, filtered images distributed on peer networks in other documented records of a campus-grade coverage have transformed personal or semi-personal material into the tool of humiliation, proving that pictorial duplication can spread the pain charged in a speed incomparable to the one of the victims of such. The time velocity of such incidences increases the distance between introduction and impact since the students who were the victims of such tragedy encounter the issue of fear, stigma, and uncertainty. Dynamics of which can be comprehended in real time thereby display how cyber threats do not move law transgression by book, but as social crises mediated in real time by the publicity and the reaction thereof. There are also second-hand reports that the instant reactions of the young people are directed towards informal certain containment but not reported containment. The first and the most obvious line of defense students tend to erase the material, lock their privacy, block the bullies, or find solace within a small circle of close people. These actions are utilitarian reaction to the speed of the platform and do not connote indifference to justice, a modeled incompatibility of an urgency of the experienced hurt with the comparatively slower cadenced institutional intervention.
Table 1
|
Table 1 Threat Mapping |
||||
|
Case
ID |
Threat
Type |
Visual
Medium Involved |
Immediate
Youth Response |
Institutional
Outcome |
|
C01 |
Image-based
harassment |
Screenshot
circulation |
Content
deletion, peer support |
Delayed
formal action |
|
C02 |
Doxxing
& surveillance |
Edited
image + profile sharing |
Privacy
restriction, blocking |
Police
complaint registered |
|
C03 |
Sexualized
trolling |
Meme
reposts |
Ignoring,
group reporting |
No
official response |
|
C04 |
Non-consensual
sharing |
Short-video
redistribution |
Emotional
withdrawal, peer counseling |
Campus
inquiry initiated |
|
C05 |
Impersonation
account |
Fake
profile visuals |
Mass
peer reporting |
Account
removed, warning issued |
Action organized in groups (such as mass reporting abusive accounts, posting messages of support online publicly) was more efficient than a channel of official complaints and meant that resultant digital communities of participation can be a makeshift protection system. At the same time, relying on informal systems may reinforce underreporting, making it possible to allow the offenders to escape even within the framework of the larger institutions. A current case evidence will therefore be telling of a dual reality where the youth agency is providing an immediate emotional/social relief without the structural justice processes being engaged to the entirety.
Table 2
|
Table 2 Variable Description |
|
|
Variable |
Meaning |
|
Threat Type |
Category
of gendered cyber harm experienced |
|
Visual Medium |
Form
of image/video/screenshot enabling circulation |
|
Youth Response |
First
coping or resistance action taken by student |
|
Institutional Outcome |
Result
of formal reporting or authority intervention |
These cases are further detailed by the institutional experience which those cases are placed under, to create further detail of how complexity is created and shaped upon because of the style of communication, the interpretation of evidence and the confidence which actually goes with the winner (in terms of survivor confidence). Being empathically written, giving clear procedural guidelines, and being aware of the potential reputational harm of graphic harm, campus authorities or cybercrime units were perceived to be more trustworthy and acceptable in setting formal resilience by the aggrieved students. Conversely, responses perceived as dismissive, technical and slow gathered feelings of isolation and stopped further communication. The visual documentation role, the screenshots, chat logs, shared pictures, etc. played an important role in mediating these interactions as evidence and testimonial narrative and violation reminders. The real-time case analysis can therefore highlight that protection of the same is not only to be effective in the legal competency terms, but is also capable of mediating a digital experience in a cultural and affective manner.
7. Results and Analysis
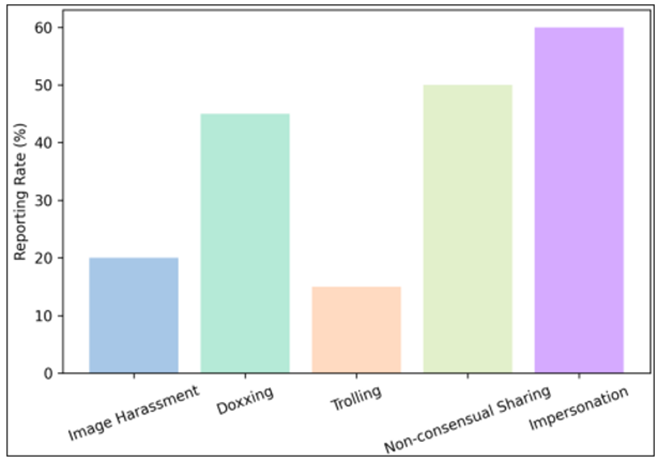
The analysis of the cases of cyber-threat observed in universities exposes periodic associations between the category of visualized harm, youth coping, the overall effect of the harm and the probability of reporting by an institution. The reporting patterns of image-based harassment and non-consent sharing, respectively, are associated with a relatively greater predisposition to reporting, indicating that tangible visual-based evidence enhances the legitimacy of perceived legitimacy of complaining and confidence in the response of the institution. The trolling driven by memes has the lowest rate of reporting, which is an indicator of the normalized phenomenon of symbolic harassment in peer culture and propensity to assign such abuse as part of social nor legally punishable. These results support the previously stated argument in that exposure to threat and interpretation of the justice pathways are both influenced by visual mediation.
Figure 5
Figure 5 Reporting Rate Across Threat Types
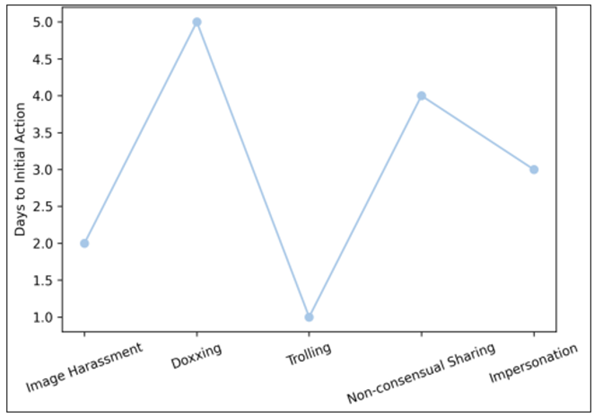
The time aspect of decision-making also explains youthful decision-making shown in Figure 5. The average time to first coping action is the shortest to trolling-related incidents and the longest to doxxing or surveillance as they are perceived as less severe and have a less significant reputational risk.
Figure 6
Figure 6 Average Response Time by Threat Type
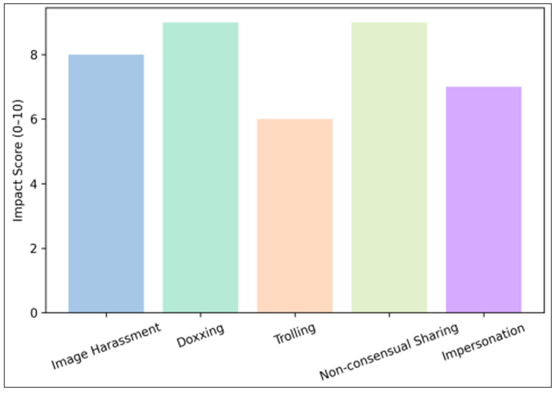
The initial informal coping (rapid) that is usually realized before any formal intervention is blocking, deletion or peer consultation, and proves the presence of a trust gap between precipitous lived harm and procedural protection. The overall scores Figure 6 in emotional impact are also consistently high in visual tenacious threats like doxxing and sharing without a person’s consent, which proves that permanence of visual circulation tends to contribute to psychological suffering irrespective of the outcomes of the reported cases.
Figure 7
Figure 7 Emotional Impact Score Across Threat Types
These patterns contribute to a stratified ecology whereby the visual pieces of evidence, the degree of emotion, and the institutional trust combine to influence reporting behaviors Figure 7. The fact that real-time analysis is in support of the greater theoretical argument that digital visual culture reorders vulnerabilities and protection paths. Youth agency is seen in the quick peer-based mitigation, but structural justice is not even triggered in the same way. The highest levels of institutional legitimacy are observed in cases where harm is easily seen and refers to familiar categories of the law, and low levels in cases where the harassment is normalized by various cultures or symbolically mediated. These forces reinstate the need to have visually sensitive, emotionally sensitive, and time-sensitive protection models that can capture the realities of youth digital life.
8. Visual Culture as a Site of Power, Risk, and Protection
Visual culture emerges as a main point of convergence between gendered cyber threats, youth perception and protection of institutions in that digital harm is not a technological or legal caring but a social interventional experience with representation, emotion, and group interpretation. In the analyses above, digital bodies seem both enabled and vulnerable in a self-presentative practice that creates an opportunity of experimenting with identity and heightens presence in surveillance-oriented and judgmental space. The empirical observations of university young people show that cyber harassment is still experienced not as a one-point situation, but rather as a stable condition, entrenched in forms of visual movement, dialogues, and fear of anticipation. These circumstances make vulnerability a structural aspect of engagement in networked public life, especially among women whose presence on the internet is often reputational and their presence is often violence of a symbolic nature. Visual mediation thus acts as both a process of injury- by exaggerating, rendering and making visible- and as well as a process of enlightenment, solidarity and resistance that can redefine safety and accountability. When viewed through this visual lens, institutional protection rather seems conditional upon the cultural resonance than on the effectuality of the procedures. The embodiment of trust in policing and social safeguards is dependent on the representation of authority through the digital discourse of youths. Structural gaps that have been established above reveal that underreporting and informal coping is predisposed to the delay in responding, legalistic communication styles, and little regard regarding affective harm. Simultaneously, counter-narratives created by young people show that protection may also be produced via participatory cultures of care that are resistant to stigma and generate collective strength. This makes visual culture a field of power that is always dynamic as the power cannot exist without vulnerability and agency, as well as the meanings of justice that are always negotiated between the lives and the institution.
9. Conclusion and Future Work
Gendered cyber threats in the context of university youths demonstrate the inextricable connection between the visual culture of digital form, embodied identity, and the perceived validity of the system of social protection. The analysis shows that online harm is not only as a discrete legal violation, but also as a sustained visual exposure which constitutes the experience of fear, reputation, participation and trust. Perceptions of youth demonstrate the misalignment in institutions and lived digital realities especially in response, communicative tone, and awareness of affective harm. Vulnerability, intensified by circulation and permanence, but also resisting, finding solidarity, and raising awareness, which broadens the notion of protection beyond enforcement, is imposed by visual mediation. Social protection thus can be conceptualized as the culturally negotiated process that involves the visual literacy, emotional sensitivity, and participatory process with youth communities. The future research area must be expanded with empirical studies of digital vulnerability in the long run and cross-culturally by employing platform governance relations, intersectional gender subjectivities, and shifting types of visual harassment including synthetic images and AI-mediated manipulation. Theoretical integration of visual studies, gender scholarship, and socio-legal analysis could be further reinforced by quantitative modeling of reporting network, trust formation, and network resilience. The creation of young-oriented visual communication systems of policing and computerized education is a significant applied focus that can help to change the level of awareness to a level of prevention as a social system. The further interdisciplinary cooperation is needed in creating responsive protection systems in accordance with quickly changing digital worlds.
CONFLICT OF INTERESTS
None.
ACKNOWLEDGMENTS
None.
REFERENCES
Angrish, K., Oshana, D., and Gammage, K. L. (2024). Flex Friday: A Content Analysis of Men’s Fitspiration on Instagram. Body Image, 48, Article 101651. https://doi.org/10.1016/j.bodyim.2023.101651
Bhandari, A., and Bimo, S. (2020). TikTok and the “Algorithmized Self”: A New Model of Online Interaction. AoIR Selected Papers of Internet Research. https://doi.org/10.5210/spir.v2020i0.11172
Biradar, D. M., Shaikh, T., and Upadhyay, D. (2025). Deepfake Detection Using Deep Learning. International Journal of Recent Advances in Engineering and Technology, 14(2s), 66–69.
Bucher, T., and Helmond, A. (2017). The Affordances of Social Media Platforms. In J. Burgess, A. Marwick, and T. Poell (Eds.), The SAGE Handbook of Social Media (233–253). SAGE Publications. https://doi.org/10.4135/9781473984066.n14
Evans, A., and Ringrose, J. (2024). More-Than-Human, More-Than-Digital: Postdigital Intimacies as a Theoretical Framework for Intimate Therapeutics and Technology-Facilitated Sexual Violence. Social Media and Society. https://doi.org/10.1177/20563051251317779
Goodyear, V., Andersson, J., Quennerstedt, M., and Varea, V. (2021). #Skinny Girls: Young Girls’ Learning Processes and Health-Related Social Media. Qualitative Research in Sport, Exercise and Health, 14, 1–18. https://doi.org/10.1080/2159676X.2021.1888152
Ringrose, J., Milne, B., Mishna, F., Regehr, K., and Slane, A. (2022). Young People's Experiences of Image-Based Sexual Harassment and Abuse in England and Canada: Toward a Feminist Framing of Technologically Facilitated Sexual Violence. Women’s Studies International Forum, 93, Article 102615. https://doi.org/10.1016/j.wsif.2022.102615
Schellewald, A. (2023). Understanding the Popularity and Affordances of TikTok through User Experiences. Media, Culture and Society, 45, 1568–1582. https://doi.org/10.1177/01634437221144562
Seguin, D., Kuenzel, E., Morton, J. B., and Duerden, E. G. (2021). School’s out: Parenting Stress and Screen Time Use in School-Age Children During the COVID-19 Pandemic. Journal of Affective Disorders Reports, 6, Article 100217. https://doi.org/10.1016/j.jadr.2021.100217
Sheth, A., Shalin, V. L., and Kursuncu, U. (2022). Defining and Detecting Toxicity on Social Media: Context and Knowledge are Key. Neurocomputing, 490, 312–318. https://doi.org/10.1016/j.neucom.2021.11.095
Whitehead, S., and Ringrose, J. (2021). Memetic Masculinities: Exploring Racialized Homosociality and Networked Misogynoir in Teen Boys’ Instagram Social Media Diaries. In F. Blaikie (Ed.), Global Perspectives on Youth and Young Adults: Situated, Embodied and Performed Ways of Being, Engaging and Belonging ( 99–121). Routledge. https://doi.org/10.4324/9781003055822-8
|
|
 This work is licensed under a: Creative Commons Attribution 4.0 International License
This work is licensed under a: Creative Commons Attribution 4.0 International License
© ShodhKosh 2026. All Rights Reserved.